From Power Lines to Passwords: The Utility Sector Must Elevate Cybersecurity to Safeguard the Grid
As utilities increasingly integrate digital technologies into their operations, the critical need for robust cybersecurity measures is pushed to the forefront. As discussed by West Monroe, the intermingling of operational technology (OT) and information technology (IT) networks reveals a landscape ripe with benefits yet fraught with emerging security threats. This blend necessitates stronger cyber defenses within the utility sector to protect the infrastructure that supports our daily lives. The International Energy Agency (IEA) adds to this conversation by highlighting the expanded cyberattack surface due to heightened connectivity and automation, pointing out the pressing need for comprehensive risk management strategies that address these vulnerabilities and bolster cybersecurity measures.
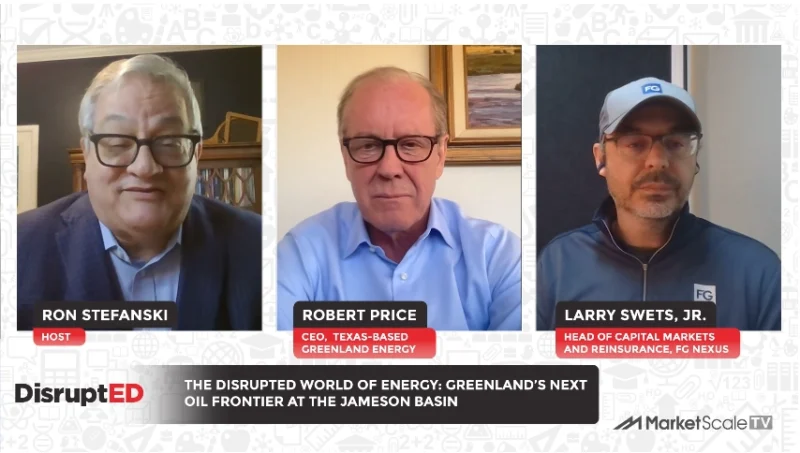
Amidst this backdrop, the secure and reliable transfer of data becomes a linchpin for utility operations, especially with the increased emphasis on renewable energy and energy storage systems. In response to these challenges, MarketScale had the opportunity to capture invaluable insights from Kuru Kuruvilla, the Industry Marketing Manager at Moxa on the show floor of DISTRIBUTECH 2024. Kuruvilla brings to the table expert perspectives on ensuring data security and reliability amidst the digital shift, offering a beacon of guidance as the utility sector navigates this complex digital terrain.
Kuruvilla’s Thoughts
“So one of the things, as you kind of see, is that utilities are using more and more data, right, you know, from a real-time perspective, and that data needs to be both reliable and secure. So reliable meaning, you know, the bandwidth of the data, you know, how frequently that data is transmitted. Secure meaning they need to be cybersecure, you know, from a perspective of, you know, intrusion detection. So if you think about that paradigm, and then if you look at the various changes that have happened in the utility side of things, for example, when a lot of growth in renewables, you have now energy storage systems which are much more critical now than it was before.
Ensure Data is Transferred in a Safe and Reliable Way
“Now, if you are an energy storage integrator, you want to make sure that all the information that is required to optimize, you know, that system, whether it’s the battery operation, battery temperatures, or whether it’s intrusion detection, whether it’s data transfer, that all needs to happen, right, in a very secure and reliable way, because now you are much more important to the grid than maybe you were, you know, three or four years back. So a lot of that has to do with digitizing, you know, the data flow, right? So meaning there is a lot less analog signals, analog wiring, going more into Ethernet, and making sure that, you know, the system can talk to each other, right? Because there are equipment of, you know, different vintages, different providers, you know, that are in the system. How do we make sure that the whole thing, right? So the whole transition, I would say, into that, you know, secure and reliable is being almost forced by the changes that are happening and the criticality that’s happening in the grid. And they are already used to, you know, creating redundant networks in an actual power system, so in an actual, you know, distribution feeder, right?”
Partner Up with IT Experts to Stay Protected
“Some of the similar principles, you know, need to happen in communication. So, for example, what happens if a certain section of that communication network gets broken? Do you have, you know, redundant protocols that are allowing you to still communicate all the critical infrastructure back, you know, into the SCADA system, for example? The other piece is, you know, from a cybersecurity standpoint, right? Do you have not just the equipment, you know, obviously critical to have the equipment already tested, but do you have the processes to manage, right, your entire, you know, IT system and still be cybersecure? So things like password management, right? Things like authentication, you know, zero-trust environments. You know, most of the utilities are not, you know, necessarily experts in IT and networking. Do you have partners, right, you know, who can help them with that? Who can help, you know, create specifications, help co-create, you know, that aspect of it so that it’s a partnership versus, you know, the utility trying to reinvent, right, the wheel every time?”
Article by Sonia Gossai